How to Protect Your Tourism Business from AI Voice Cloning Scams

In a recent open Q&A Tourism Tech Session, tourism operators could ask anything. The topic that really stood out as needing to be addressed was scams and security for your tourism business. AI voice cloning tools can replicate someone’s voice from as little as three seconds of audio, and Australian telcos have no technical mechanism to block spoofed caller IDs. This post covers the practical steps every tourism business owner needs to take now to protect themselves, their team, and their customers.
This was an open Q&A Tourism Tech session and was not recorded.
Quick links
- What are Tourism Tech Sessions?
- What is AI voice cloning and why does it matter?
- Why Australian telcos cannot stop spoofed calls
- How to set up a safe word for your family and team
- Why email is not a safe place for credentials or passports
- The digital trust advantage for tourism brands
- Things to try this week
What are Tourism Tech Sessions?
Our Tourism Tech Sessions are twice monthly group coaching calls designed to support AI Enablement Plan members, whether you’re a direct member or a participant of one of our tourism digital capability programs. These sessions provide a space to:
- Learn the latest developments in tourism tech
- Ask questions in a safe, supportive environment
- Hear real-life examples and get practical demos
- Get the confidence to implement what you’ve learned
If you’re not a member, this article will walk you through the key takeaways. Join an AI Enablement Plan to access future Tourism Tech Sessions and have an expert at your fingertips to ask your business-specific questions.
What is AI voice cloning and why does it matter?
AI voice cloning tools generate a convincing replica of someone’s voice using as little as three seconds of audio. Scammers are already using this to impersonate family members, business owners, and staff in phone calls, asking for urgent bank transfers or account access.
This came up in a recent session because Fabienne had demonstrated how AI twin tools work: upload a headshot and a short voice recording, and the tool creates a digital avatar that looks and sounds like you. Attendees immediately saw the other side. If we can do this in minutes with free tools, so can anyone.
Around 50% of social media content is now estimated to feature AI-generated avatars. This is not experimental technology. Tourism business owners who make video content, appear in reels, or have their voice publicly available online are the exact profile these scammers target.
Why Australian telcos cannot stop spoofed calls
Phone number spoofing lets a caller display any number they choose on your screen, including numbers belonging to your bank, a government agency, or someone you know. Australian telecommunications providers currently have no equivalent to email’s SPF and DKIM protocols to verify that a caller is who they claim to be.
Email phishing has been reduced significantly because authentication standards let receiving servers verify the sender’s identity. No comparable standard exists for Australian phone calls at scale. If someone calls from what appears to be your accountant’s number and asks you to transfer funds urgently, there is no automated system to confirm the call is genuine.
A security app or a premium telco plan will not close this gap. It is a structural limitation of the current phone system. The only effective defence right now is behavioural.
How to set up a safe word for your family and team
A safe word is a pre-agreed code word that anyone calling to verify their identity must provide before you act on any request involving money, access, or personal information. Fabienne raised this in the session as a direct, low-cost defence against voice cloning scams targeting families and small businesses.
Set one up with your immediate family and your key team members. The word should be memorable but not guessable from your public social media profiles. If someone calls claiming to be your partner, your child, or your accountant and cannot provide the safe word, hang up and call that person back on a number you already have saved.
The same principle applies to your business. If a supplier or team member calls requesting an urgent payment or a credential reset, require them to verify via a second channel before you act. A message to their known number or a quick check on Slack takes thirty seconds and removes most social engineering risk.
Why email is not a safe place for credentials or passports
Email is not encrypted in transit by default. Passwords, passport scans, and bank account details sent via email can be intercepted, forwarded, or accessed by anyone who gains entry to either inbox. The session discussion made clear that emailing sensitive documents is still common practice for tourism businesses managing staff onboarding and supplier relationships.
A password manager such as 1Password lets you share credentials with team members without ever sending a password in plain text. The recipient gets access through the tool. When a staff member leaves, you revoke their access from one place rather than hunting through email threads for every shared password.
For documents like passport scans and tax file numbers, use a secure file-sharing service rather than email attachments. Google Drive with restricted sharing, a dedicated HR platform, or a secure document portal all provide better protection. Once a document is in an email thread, you have no control over where it goes next.
The digital trust advantage for tourism brands
As AI-generated content becomes harder to distinguish from authentic content, the businesses that invest in verifiable authenticity will have an advantage. Consumers are already becoming more sceptical of content that looks too polished or too generic.
Tourism operators who show up consistently as themselves – real faces, real voices, real behind-the-scenes content – are building what the session described as a “digital trust tax”: the premium people are willing to pay to book with someone they recognise and trust over an anonymous listing. AI-generated content cannot replicate this.
Being transparent about your AI use contributes to this. Declaring AI-generated images in your terms and conditions, adding SynthID watermarks to AI content, and being honest about how you use these tools builds credibility over time. Customers do not expect zero AI use. They expect honesty.
Things to try this week
- Set up a safe word with your immediate family and at least one key team member. Choose something memorable that is not visible on your public social media profiles.
- Audit your email habits. If you have sent any passwords, passport scans, or financial credentials via email in the past year, change those passwords now and move future sharing to a secure channel.
- Set up a password manager such as 1Password for your business. Start with your most-used platforms: booking systems, social media accounts, and accounting software.
- Search your own name and business name on social media to check whether any AI-generated content using your likeness is already in circulation. Report anything that misrepresents you.
- Update your internal process for urgent payment requests. Any request for a bank transfer received by phone or email should require a callback to a saved number before it is actioned.
Want to get your tourism business more visible online?
Staying secure online and being genuinely visible to AI tools go hand in hand. Tourism Tribe offers three ways to help:
- GEO Assessment: find out how visible your business is to AI tools right now
- Digital Direction Plan: a personalised roadmap for your digital and AI strategy
- AI Enablement Plans: ongoing access to Tourism Tech Sessions, tools, and hands-on support
Can AI tools really clone someone’s voice?
AI voice cloning tools can generate a convincing replica of someone’s voice using as little as three seconds of publicly available audio. Tools that create AI digital avatars and voice clones are freely accessible online, not restricted to specialists. Scammers use cloned voices in phone calls to impersonate family members or business contacts and request urgent transfers or account access.
What is phone number spoofing?
Phone number spoofing is when a caller deliberately displays a different phone number on the recipient’s screen. Australian telecommunications providers currently have no technical mechanism equivalent to email authentication standards to verify that a caller’s displayed number is genuine. This means a scammer’s call can appear to come from your bank, your accountant, or a family member.
What is a safe word and how do I use one to protect my business?
A safe word is a code word you agree on in advance with family members or key team members. When someone calls claiming to be a known person and asks you to act urgently on a request involving money or account access, you ask for the safe word before taking any action. If they cannot provide it, hang up and call the person back on their saved number to verify the request.
Is it safe to email passwords or passport scans?
Email is not encrypted in transit by default, which means passwords, passport scans, and financial documents sent by email can be intercepted or accessed if either inbox is compromised. Use a password manager such as 1Password to share credentials with team members, and a secure file-sharing service for sensitive documents rather than email attachments.
How can a tourism business build digital trust as AI content becomes more common?
Tourism businesses build digital trust by showing up consistently as real people with real voices and real experiences rather than relying on AI-generated content alone. Being transparent about AI use, declaring AI-generated images in your terms and conditions, and using verification tools like SynthID all signal to potential customers that your content is genuine. Customers do not expect zero AI use – they expect honesty about it.
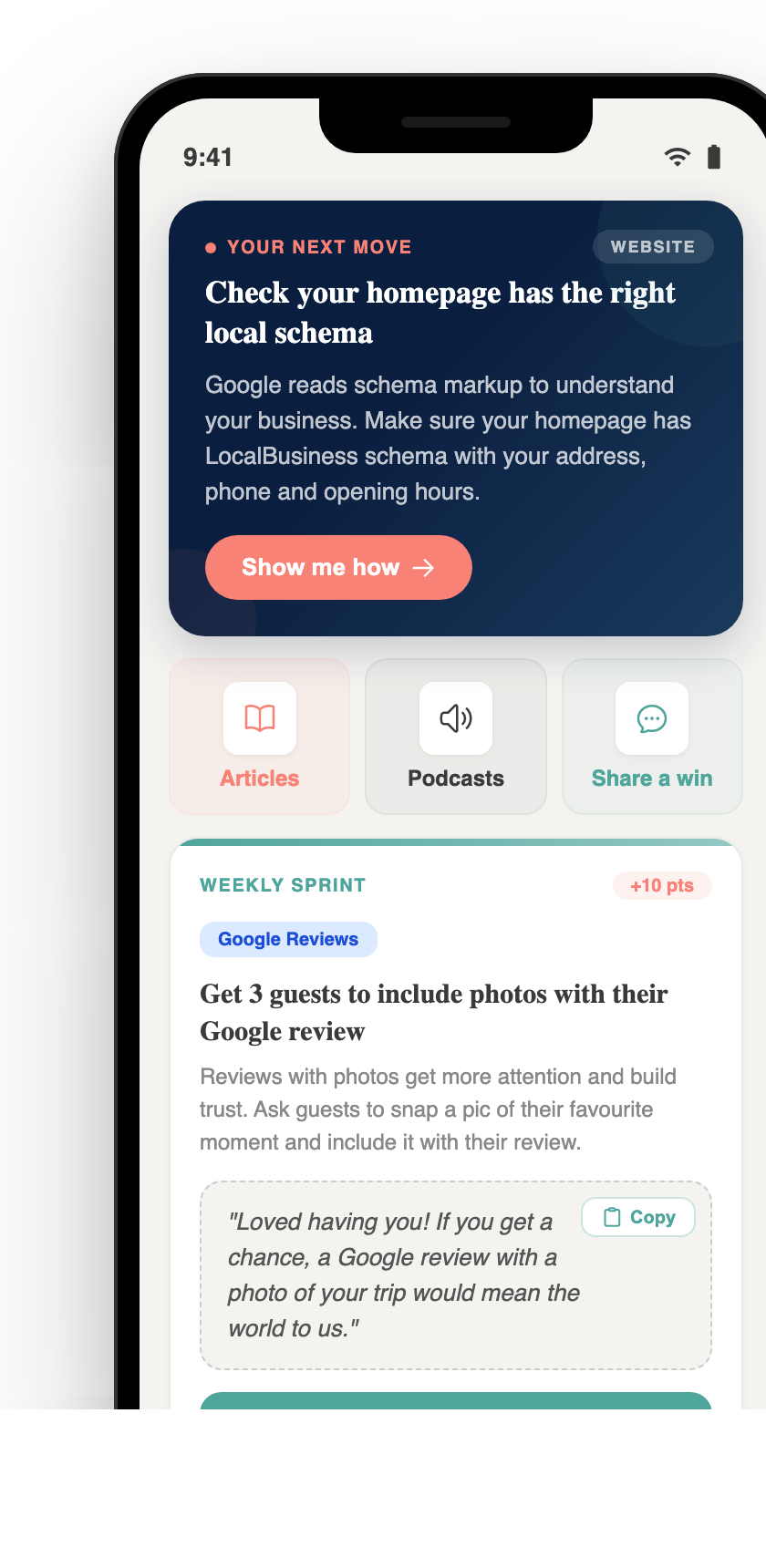
Your free AI marketing coach, right in your pocket
The free Pocket Rocket app gives you a personal AI marketing coach, website audit, weekly action plans and 5-minute tips. Built for tourism operators.